Particular because of Vlad Zamfir, Chris Barnett and Dominic Williams for concepts and inspiration
In a current weblog publish I outlined some partial options to scalability, all of which match into the umbrella of Ethereum 1.0 because it stands. Specialised micropayment protocols equivalent to channels and probabilistic fee methods could possibly be used to make small funds, utilizing the blockchain both just for eventual settlement, or solely probabilistically. For some computation-heavy purposes, computation could be performed by one occasion by default, however in a approach that may be “pulled down” to be audited by all the chain if somebody suspects malfeasance. Nonetheless, these approaches are all essentially application-specific, and much from excellent. On this publish, I describe a extra complete method, which, whereas coming at the price of some “fragility” considerations, does present an answer which is far nearer to being common.
Understanding the Goal
To begin with, earlier than we get into the main points, we have to get a a lot deeper understanding of what we truly need. What can we imply by scalability, significantly in an Ethereum context? Within the context of a Bitcoin-like foreign money, the reply is comparatively easy; we wish to have the ability to:
- Course of tens of 1000’s of transactions per second
- Present a transaction price of lower than $0.001
- Do all of it whereas sustaining safety in opposition to a minimum of 25% assaults and with out extremely centralized full nodes
The primary purpose alone is straightforward; we simply take away the block dimension restrict and let the blockchain naturally develop till it turns into that enormous, and the financial system takes care of itself to drive smaller full nodes to proceed to drop out till the one three full nodes left are run by GHash.io, Coinbase and Circle. At that time, some stability will emerge between charges and dimension, as excessize dimension results in extra centralization which results in extra charges because of monopoly pricing. To be able to obtain the second, we are able to merely have many altcoins. To attain all three mixed, nonetheless, we have to break by a basic barrier posed by Bitcoin and all different current cryptocurrencies, and create a system that works with out the existence of any “full nodes” that have to course of each transaction.
In an Ethereum context, the definition of scalability will get just a little extra difficult. Ethereum is, basically, a platform for “dapps”, and inside that mandate there are two sorts of scalability which are related:
- Permit heaps and plenty of individuals to construct dapps, and maintain the transaction charges low
- Permit every particular person dapp to be scalable in line with a definition much like that for Bitcoin
The primary is inherently simpler than the second. The one property that the “construct heaps and plenty of alt-Etherea” method doesn’t have is that every particular person alt-Ethereum has comparatively weak safety; at a dimension of 1000 alt-Etherea, each can be weak to a 0.1% assault from the standpoint of the entire system (that 0.1% is for externally-sourced assaults; internally-sourced assaults, the equal of GHash.io and Discus Fish colluding, would take solely 0.05%). If we are able to discover a way for all alt-Etherea to share consensus power, eg. some model of merged mining that makes every chain obtain the power of all the pack with out requiring the existence of miners that learn about all chains concurrently, then we might be performed.
The second is extra problematic, as a result of it results in the identical fragility property that arises from scaling Bitcoin the foreign money: if each node sees solely a small a part of the state, and arbitrary quantities of BTC can legitimately seem in any a part of the state originating from any a part of the state (such fungibility is a part of the definition of a foreign money), then one can intuitively see how forgery assaults may unfold by the blockchain undetected till it’s too late to revert every part with out substantial system-wide disruption through a world revert.
Reinventing the Wheel
We’ll begin off by describing a comparatively easy mannequin that does present each sorts of scalability, however supplies the second solely in a really weak and dear approach; basically, we have now simply sufficient intra-dapp scalability to make sure asset fungibility, however not rather more. The mannequin works as follows:
Suppose that the worldwide Ethereum state (ie. all accounts, contracts and balances) is break up up into N components (“substates”) (suppose 10 <= N <= 200). Anybody can arrange an account on any substate, and one can ship a transaction to any substate by including a substate quantity flag to it, however bizarre transactions can solely ship a message to an account in the identical substate because the sender. Nonetheless, to make sure safety and cross-transmissibility, we add some extra options. First, there may be additionally a particular “hub substate”, which incorporates solely an inventory of messages, of the shape [dest_substate, address, value, data]. Second, there may be an opcode CROSS_SEND, which takes these 4 parameters as arguments, and sends such a one-way message enroute to the vacation spot substate.
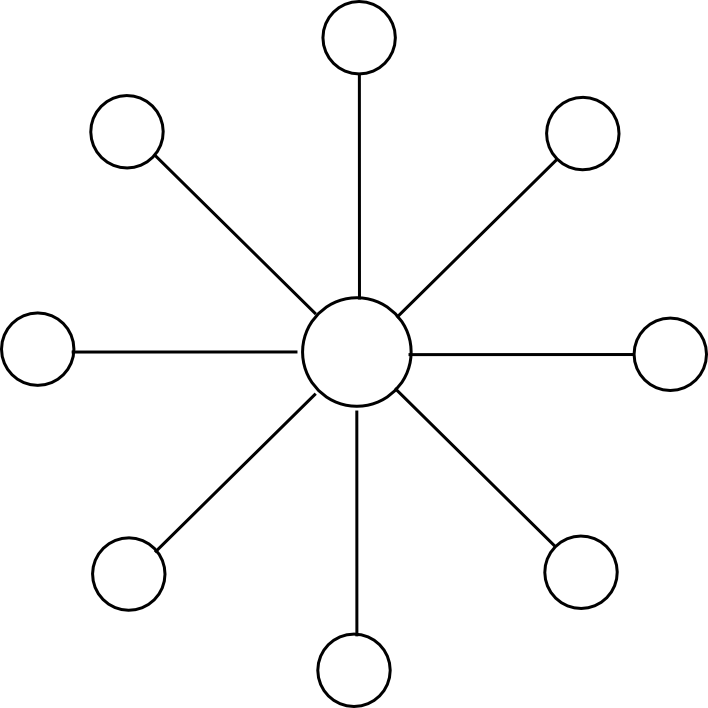
Miners mine blocks on some substate s[j], and every block on s[j] is concurrently a block within the hub chain. Every block on s[j] has as dependencies the earlier block on s[j] and the earlier block on the hub chain. For instance, with N = 2, the chain would look one thing like this:
The block-level state transition perform, if mining on substate s[j], does three issues:
- Processes state transitions within s[j]
- If any of these state transitions creates a CROSS_SEND, provides that message to the hub chain
- If any messages are on the hub chain with dest_substate = j, removes the messages from the hub chain, sends the messages to their vacation spot addresses on s[j], and processes all ensuing state transitions
From a scalability perspective, this offers us a considerable enchancment. All miners solely want to pay attention to two out of the entire N + 1 substates: their very own substate, and the hub substate. Dapps which are small and self-contained will exist on one substate, and dapps that wish to exist throughout a number of substates might want to ship messages by the hub. For instance a cross-substate foreign money dapp would preserve a contract on all substates, and every contract would have an API that permits a person to destroy foreign money items inside of 1 substate in change for the contract sending a message that may result in the person being credited the identical quantity on one other substate.
Messages going by the hub do must be seen by each node, so these might be costly; nonetheless, within the case of ether or sub-currencies we solely want the switch mechanism for use often for settlement, doing off-chain inter-substate change for many transfers.
Assaults, Challenges and Responses
Now, allow us to take this easy scheme and analyze its safety properties (for illustrative functions, we’ll use N = 100). To begin with, the scheme is safe in opposition to double-spend assaults as much as 50% of the entire hashpower; the reason being that each sub-chain is actually merge-mined with each different sub-chain, with every block reinforcing the safety of all sub-chains concurrently.
Nonetheless, there are extra harmful lessons of assaults as properly. Suppose {that a} hostile attacker with 4% hashpower jumps onto one of many substates, thereby now comprising 80% of the mining energy on it. Now, that attacker mines blocks which are invalid – for instance, the attacker features a state transition that creates messages sending 1000000 ETH to each different substate out of nowhere. Different miners on the identical substate will acknowledge the hostile miner’s blocks as invalid, however that is irrelevant; they’re solely a really small a part of the entire community, and solely 20% of that substate. The miners on different substates do not know that the attacker’s blocks are invalid, as a result of they haven’t any data of the state of the “captured substate”, so at first look it appears as if they may blindly settle for them.
Thankfully, right here the answer right here is extra advanced, however nonetheless properly inside the attain of what we at present know works: as quickly as one of many few legit miners on the captured substate processes the invalid block, they are going to see that it is invalid, and due to this fact that it is invalid in some explicit place. From there, they are going to be capable of create a light-client Merkle tree proof exhibiting that that individual a part of the state transition was invalid. To elucidate how this works in some element, a lightweight shopper proof consists of three issues:
- The intermediate state root that the state transition began from
- The intermediate state root that the state transition ended at
- The subset of Patricia tree nodes which are accessed or modified within the strategy of executing the state transition
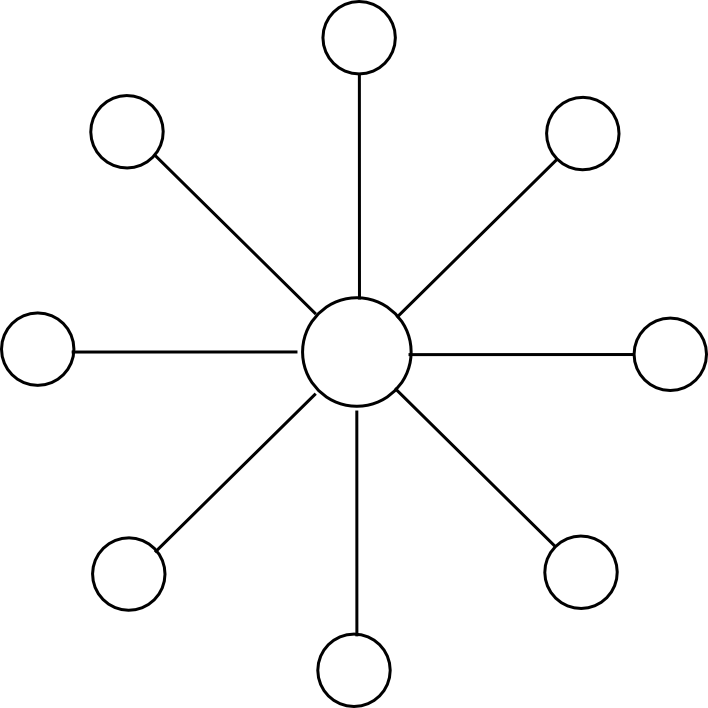
The primary two “intermediate state roots” are the roots of the Ethereum Patricia state tree earlier than and after executing the transaction; the Ethereum protocol requires each of those to be in each block. The Patricia state tree nodes offered are wanted with the intention to the verifier to comply with alongside the computation themselves, and see that the identical result’s arrived on the finish. For instance, if a transaction finally ends up modifying the state of three accounts, the set of tree nodes that may must be offered may look one thing like this:
Technically, the proof ought to embody the set of Patricia tree nodes which are wanted to entry the intermediate state roots and the transaction as properly, however that is a comparatively minor element. Altogether, one can consider the proof as consisting of the minimal quantity of data from the blockchain wanted to course of that individual transaction, plus some further nodes to show that these bits of the blockchain are literally within the present state. As soon as the whistleblower creates this proof, they are going to then be broadcasted to the community, and all different miners will see the proof and discard the faulty block.
The toughest class of assault of all, nonetheless, is what is named a “knowledge unavailability assault”. Right here, think about that the miner sends out solely the block header to the community, in addition to the checklist of messages so as to add to the hub, however doesn’t present any of the transactions, intermediate state roots or anything. Now, we have now an issue. Theoretically, it’s totally attainable that the block is totally legit; the block might have been correctly constructed by gathering some transactions from a number of millionaires who occurred to be actually beneficiant. In actuality, in fact, this isn’t the case, and the block is a fraud, however the truth that the info is just not obtainable in any respect makes it unimaginable to assemble an affirmative proof of the fraud. The 20% trustworthy miners on the captured substate might yell and squeal, however they haven’t any proof in any respect, and any protocol that did heed their phrases would essentially fall to a 0.2% denial-of-service assault the place the miner captures 20% of a substate and pretends that the opposite 80% of miners on that substate are conspiring in opposition to him.
To unravel this drawback, we’d like one thing known as a challenge-response protocol. Basically, the mechanism works as follows:
- Sincere miners on the captured substate see the header-only block.
- An trustworthy miner sends out a “problem” within the type of an index (ie. a quantity).
- If the producer of the block can submit a “response” to the problem, consisting of a light-client proof that the transaction execution on the given index was executed legitimately (or a proof that the given index is larger than the variety of transactions within the block), then the problem is deemed answered.
- If a problem goes unanswered for a number of seconds, miners on different substates think about the block suspicious and refuse to mine on it (the game-theoretic justification for why is identical as all the time: as a result of they think that others will use the identical technique, and there’s no level mining on a substate that may quickly be orphaned)
Observe that the mechanism requires a number of added complexities on order to work. If a block is revealed alongside all of its transactions apart from a number of, then the challenge-response protocol might shortly undergo all of them and discard the block. Nonetheless, if a block was revealed actually headers-only, then if the block contained lots of of transactions, lots of of challenges can be required. One heuristic method to fixing the issue is that miners receiving a block ought to privately decide some random nonces, ship out a number of challenges for these nonces to some recognized miners on the doubtless captured substate, and if responses to all challenges don’t come again instantly deal with the block as suspect. Observe that the miner does NOT broadcast the problem publicly – that may give a chance for an attacker to shortly fill within the lacking knowledge.
The second drawback is that the protocol is weak to a denial-of-service assault consisting of attackers publishing very very many challenges to legit blocks. To unravel this, making a problem ought to have some price – nonetheless, if this price is simply too excessive then the act of creating a problem would require a really excessive “altruism delta”, maybe so excessive that an assault will finally come and nobody will problem it. Though some could also be inclined to unravel this with a market-based method that locations accountability for making the problem on no matter events find yourself robbed by the invalid state transition, it’s price noting that it is attainable to provide you with a state transition that generates new funds out of nowhere, stealing from everybody very barely through inflation, and in addition compensates rich coin holders, making a theft the place there is no such thing as a concentrated incentive to problem it.
For a foreign money, one “simple answer” is capping the worth of a transaction, making all the drawback have solely very restricted consequence. For a Turing-complete protocol the answer is extra advanced; the very best approaches probably contain each making challenges costly and including a mining reward to them. There might be a specialised group of “problem miners”, and the idea is that they are going to be detached as to which challenges to make, so even the tiniest altruism delta, enforced by software program defaults, will drive them to make right challenges. One might even attempt to measure how lengthy challenges take to get responded, and extra extremely reward those that take longer.
The Twelve-Dimensional Hypercube
Observe: that is NOT the identical because the erasure-coding Borg dice. For more information on that, see right here: https://weblog.ethereum.org/2014/08/16/secret-sharing-erasure-coding-guide-aspiring-dropbox-decentralizer/
We will see two flaws within the above scheme. First, the justification that the challenge-response protocol will work is fairly iffy at greatest, and has poor degenerate-case conduct: a substate takeover assault mixed with a denial of service assault stopping challenges might probably drive an invalid block into a sequence, requiring an eventual day-long revert of all the chain when (if?) the smoke clears. There may be additionally a fragility part right here: an invalid block in any substate will invalidate all subsequent blocks in all substates. Second, cross-substate messages should nonetheless be seen by all nodes. We begin off by fixing the second drawback, then proceed to point out a attainable protection to make the primary drawback barely much less dangerous, after which lastly get round to fixing it utterly, and on the similar time eliminating proof of labor.
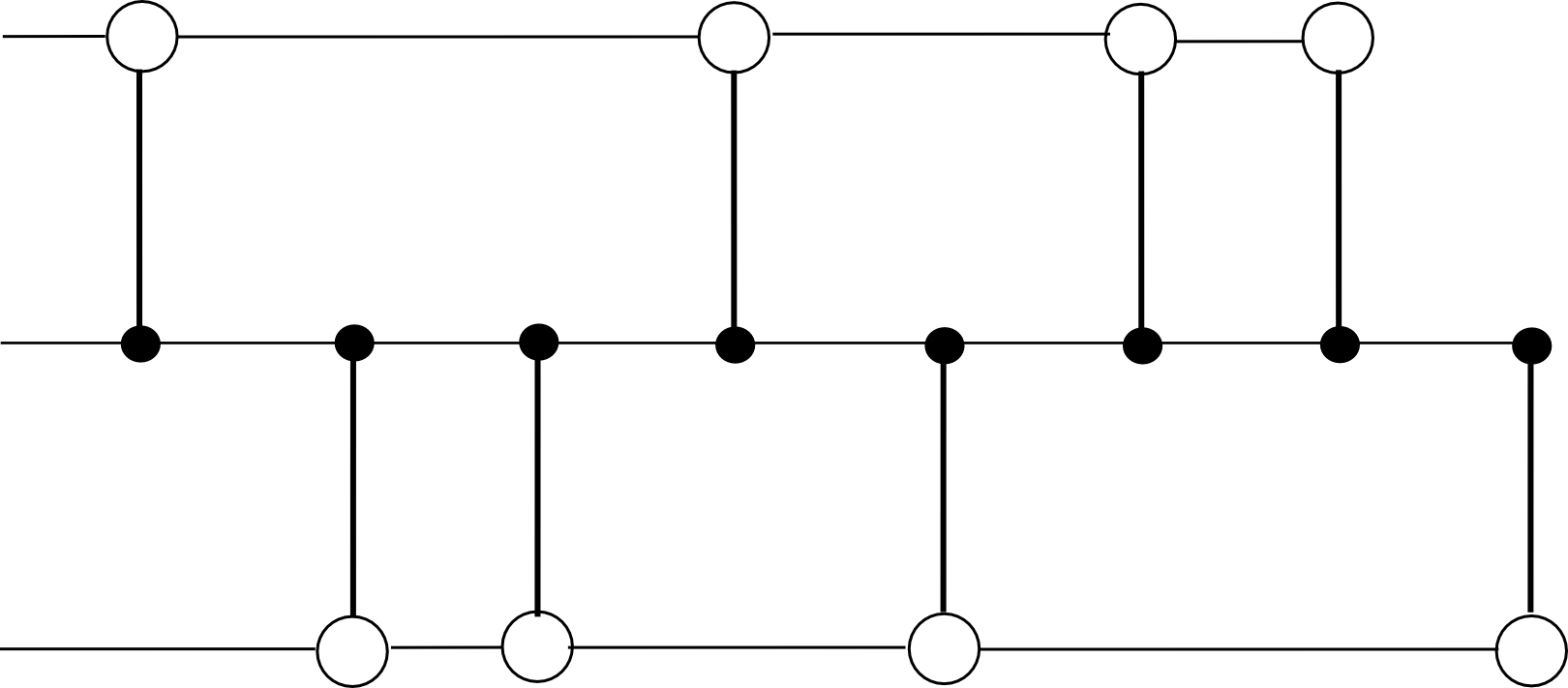
The second flaw, the expensiveness of cross-substate messages, we resolve by changing the blockchain mannequin from this:
To this:
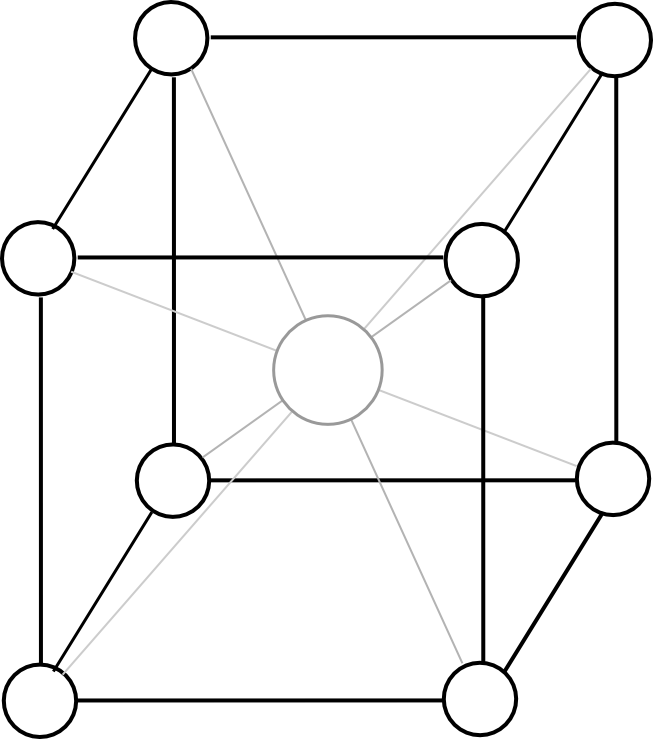
Besides the dice ought to have twelve dimensions as an alternative of three. Now, the protocol seems as follows:
- There exist 2N substates, every of which is recognized by a binary string of size N (eg. 0010111111101). We outline the Hamming distance H(S1, S2) because the variety of digits which are completely different between the IDs of substates S1 and S2 (eg. HD(00110, 00111) = 1, HD(00110, 10010) = 2, and so on).
- The state of every substate shops the bizarre state tree as earlier than, but additionally an outbox.
- There exists an opcode, CROSS_SEND, which takes 4 arguments [dest_substate, to_address, value, data], and registers a message with these arguments within the outbox of S_from the place S_from is the substate from which the opcode was known as
- All miners should “mine an edge”; that’s, legitimate blocks are blocks which modify two adjoining substates S_a and S_b, and might embody transactions for both substate. The block-level state transition perform is as follows:
- Course of all transactions so as, making use of the state transitions to S_a or S_b as wanted.
- Course of all messages within the outboxes of S_a and S_b so as. If the message is within the outbox of S_a and has last vacation spot S_b, course of the state transitions, and likewise for messages from S_b to S_a. In any other case, if a message is in S_a and HD(S_b, msg.dest) < HD(S_a, msg.dest), transfer the message from the outbox of S_a to the outbox of S_b, and likewise vice versa.
- There exists a header chain protecting observe of all headers, permitting all of those blocks to be merge-mined, and protecting one centralized location the place the roots of every state are saved.
Basically, as an alternative of travelling by the hub, messages make their approach across the substates alongside edges, and the continuously lowering Hamming distance ensures that every message all the time finally will get to its vacation spot.
The important thing design resolution right here is the association of all substates right into a hypercube. Why was the dice chosen? One of the simplest ways to think about the dice is as a compromise between two excessive choices: on the one hand the circle, and alternatively the simplex (principally, 2N-dimensional model of a tetrahedron). In a circle, a message would want to journey on common 1 / 4 of the way in which throughout the circle earlier than it will get to its vacation spot, that means that we make no effectivity beneficial properties over the plain previous hub-and-spoke mannequin.
In a simplex, each pair of substates has an edge, so a cross-substate message would get throughout as quickly as a block between these two substates is produced. Nonetheless, with miners choosing random edges it could take a very long time for a block on the proper edge to look, and extra importantly customers watching a selected substate would must be a minimum of gentle purchasers on each different substate with the intention to validate blocks which are related to them. The hypercube is an ideal stability – every substate has a logarithmically rising variety of neighbors, the size of the longest path grows logarithmically, and block time of any explicit edge grows logarithmically.
Observe that this algorithm has basically the identical flaws because the hub-and-spoke method – specifically, that it has dangerous degenerate-case conduct and the economics of challenge-response protocols are very unclear. So as to add stability, one method is to switch the header chain considerably.
Proper now, the header chain may be very strict in its validity necessities – if any block wherever down the header chain seems to be invalid, all blocks in all substates on high of which are invalid and have to be redone. To mitigate this, we are able to require the header chain to easily maintain observe of headers, so it could actually include each invalid headers and even a number of forks of the identical substate chain. So as to add a merge-mining protocol, we implement exponential subjective scoring however utilizing the header chain as an absolute widespread timekeeper. We use a low base (eg. 0.75 as an alternative of 0.99) and have a most penalty issue of 1 / 2N to take away the profit from forking the header chain; for these not properly versed within the mechanics of ESS, this principally means “enable the header chain to include all headers, however use the ordering of the header chain to penalize blocks that come later with out making this penalty too strict”. Then, we add a delay on cross-substate messages, so a message in an outbox solely turns into “eligible” if the originating block is a minimum of a number of dozen blocks deep.
Proof of Stake
Now, allow us to work on porting the protocol to nearly-pure proof of stake. We’ll ignore nothing-at-stake points for now; Slasher-like protocols plus exponential subjective scoring can resolve these considerations, and we’ll focus on including them in later. Initially, our goal is to point out make the hypercube work with out mining, and on the similar time partially resolve the fragility drawback. We’ll begin off with a proof of exercise implementation for multichain. The protocol works as follows:
- There exist 2N substates indentified by binary string, as earlier than, in addition to a header chain (which additionally retains observe of the newest state root of every substate).
- Anybody can mine an edge, as earlier than, however with a decrease problem. Nonetheless, when a block is mined, it have to be revealed alongside the entire set of Merkle tree proofs so {that a} node with no prior info can totally validate all state transitions within the block.
- There exists a bonding protocol the place an deal with can specify itself as a possible signer by submitting a bond of dimension B (richer addresses might want to create a number of sub-accounts). Potential signers are saved in a specialised contract C[s] on every substate s.
- Primarily based on the block hash, a random 200 substates s[i] are chosen, and a search index 0 <= ind[i] < 2^160 is chosen for every substate. Outline signer[i] because the proprietor of the primary deal with in C[s[i]] after index ind[i]. For the block to be legitimate, it have to be signed by a minimum of 133 of the set signer[0] … signer[199].
To really examine the validity of a block, the consensus group members would do two issues. First, they’d examine that the preliminary state roots offered within the block match the corresponding state roots within the header chain. Second, they’d course of the transactions, and guarantee that the ultimate state roots match the ultimate state roots offered within the header chain and that each one trie nodes wanted to calculate the replace can be found someplace within the community. If each checks cross, they signal the block, and if the block is signed by sufficiently many consensus group members it will get added to the header chain, and the state roots for the 2 affected blocks within the header chain are up to date.
And that is all there may be to it. The important thing property right here is that each block has a randomly chosen consensus group, and that group is chosen from the worldwide state of all account holders. Therefore, until an attacker has a minimum of 33% of the stake in all the system, it is going to be nearly unimaginable (particularly, 2-70 likelihood, which with 230 proof of labor falls properly into the realm of cryptographic impossiblity) for the attacker to get a block signed. And with out 33% of the stake, an attacker won’t be able to forestall legit miners from creating blocks and getting them signed.
This method has the profit that it has good degenerate-case conduct; if a denial-of-service assault occurs, then likelihood is that just about no blocks might be produced, or a minimum of blocks might be produced very slowly, however no injury might be performed.
Now, the problem is, how can we additional cut back proof of labor dependence, and add in blockmaker and Slasher-based protocols? A easy method is to have a separate blockmaker protocol for each edge, simply as within the single-chain method. To incentivize blockmakers to behave truthfully and never double-sign, Slasher may also be used right here: if a signer indicators a block that finally ends up not being in the primary chain, they get punished. Schelling level results be certain that everybody has the inducement to comply with the protocol, as they guess that everybody else will (with the extra minor pseudo-incentive of software program defaults to make the equilibrium stronger).
A full EVM
These protocols enable us to ship one-way messages from one substate to a different. Nonetheless, a method messages are restricted in performance (or fairly, they’ve as a lot performance as we wish them to have as a result of every part is Turing-complete, however they don’t seem to be all the time the nicest to work with). What if we are able to make the hypercube simulate a full cross-substate EVM, so you’ll be able to even name capabilities which are on different substates?
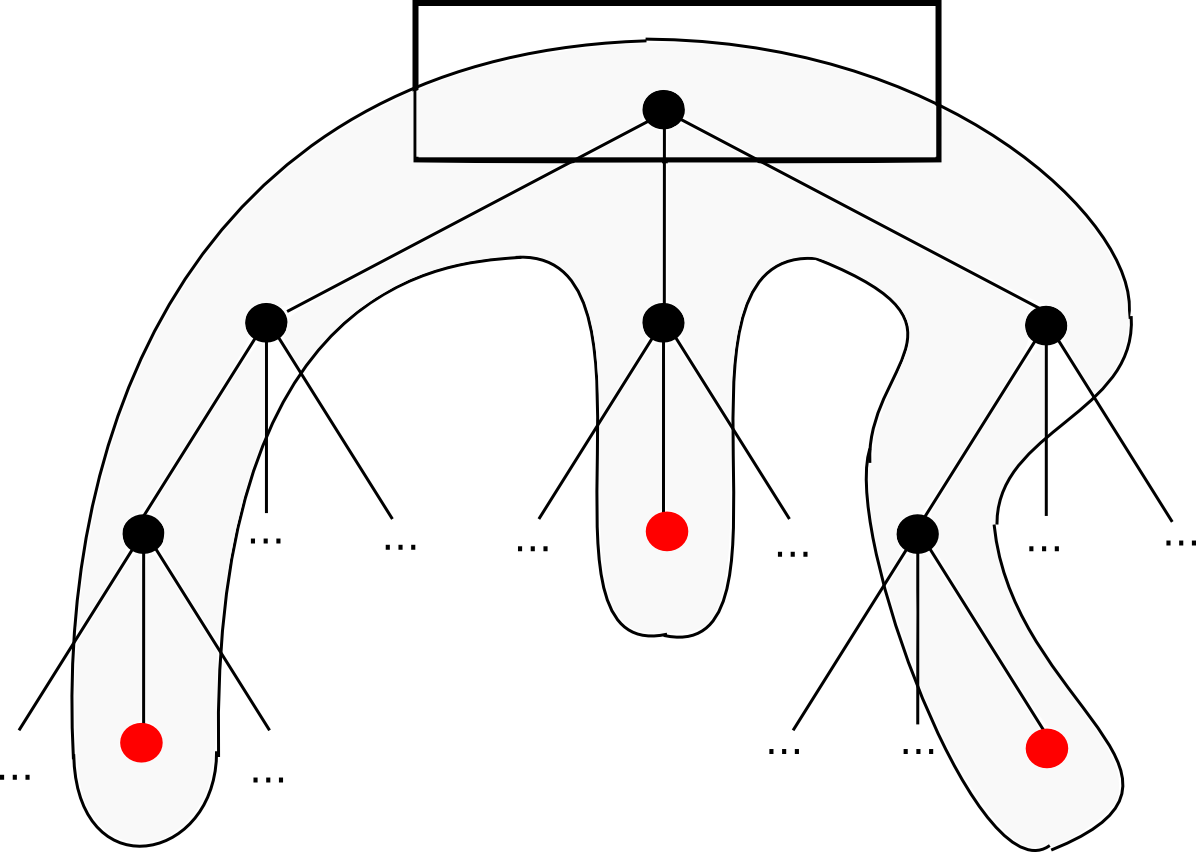
Because it seems, you’ll be able to. The bottom line is so as to add to messages an information construction known as a continuation. For instance, suppose that we’re in the midst of a computation the place a contract calls a contract which creates a contract, and we’re at present executing the code that’s creating the internal contract. Thus, the place we’re within the computation seems one thing like this:
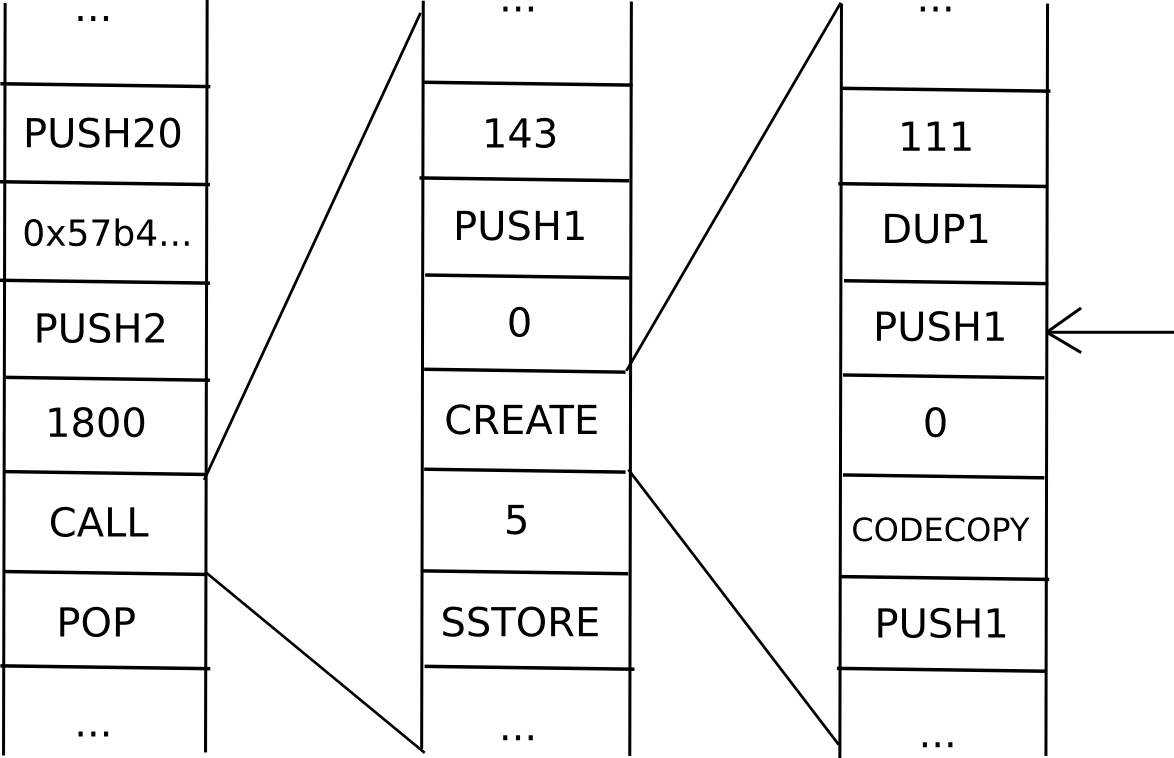
Now, what’s the present “state” of this computation? That’s, what’s the set of all the info that we’d like to have the ability to pause the computation, after which utilizing the info resume it afterward? In a single occasion of the EVM, that is simply this system counter (ie. the place we’re within the code), the reminiscence and the stack. In a scenario with contracts calling one another, we’d like that knowledge for all the “computational tree”, together with the place we’re within the present scope, the dad or mum scope, the dad or mum of that, and so forth again to the unique transaction:
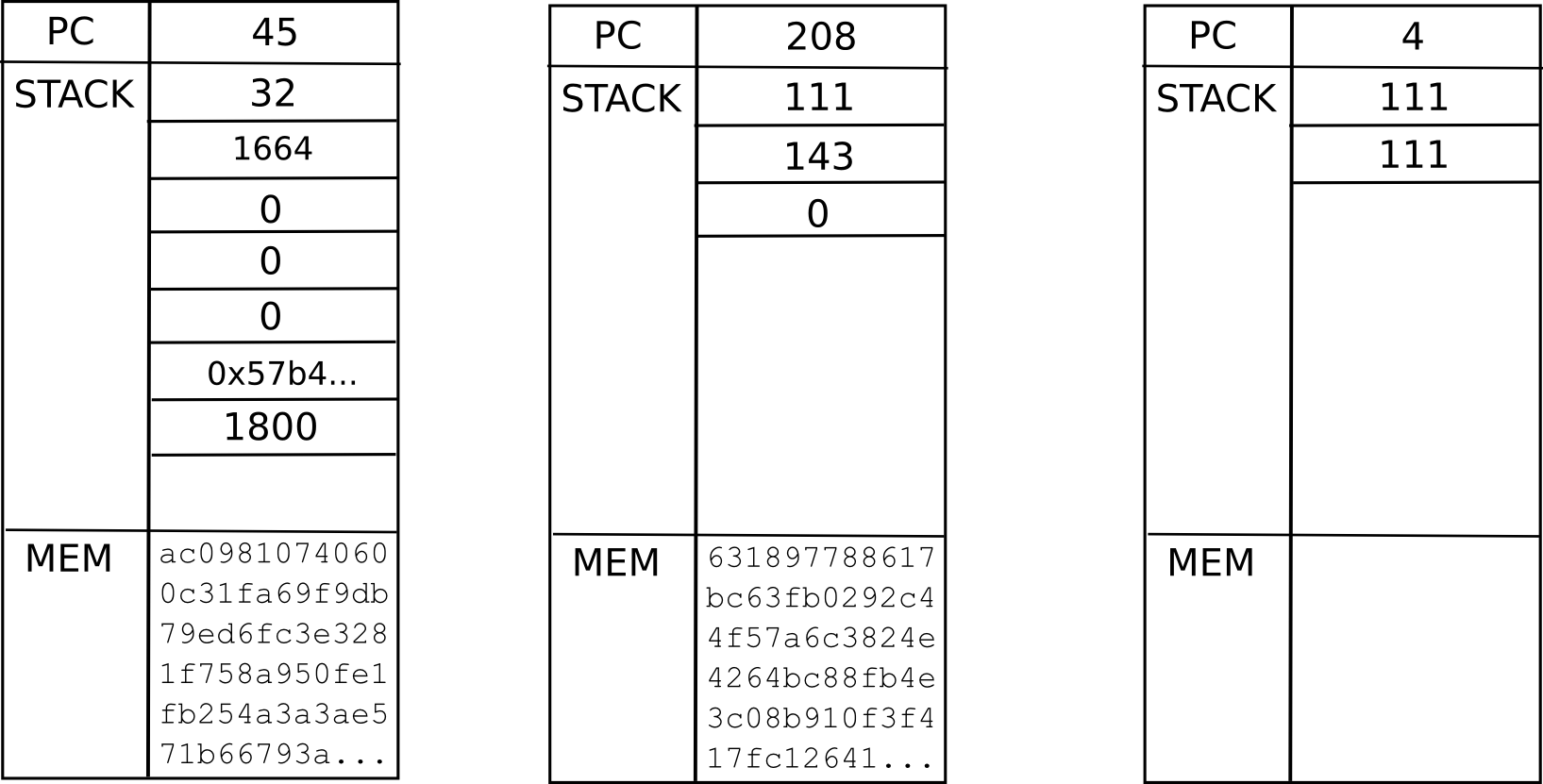
That is known as a “continuation”. To renew an execution from this continuation, we merely resume every computation and run it to completion in reverse order (ie. end the innermost first, then put its output into the suitable house in its dad or mum, then end the dad or mum, and so forth). Now, to make a totally scalable EVM, we merely exchange the idea of a one-way message with a continuation, and there we go.
In fact, the query is, can we even wish to go this far? To begin with, going between substates, such a digital machine can be extremely inefficient; if a transaction execution must entry a complete of ten contracts, and every contract is in some random substate, then the method of operating by that whole execution will take a mean of six blocks per transmission, instances two transmissions per sub-call, instances ten sub-calls – a complete of 120 blocks. Moreover, we lose synchronicity; if A calls B as soon as after which once more, however between the 2 calls C calls B, then C can have discovered B in {a partially} processed state, probably opening up safety holes. Lastly, it is troublesome to mix this mechanism with the idea of reverting transaction execution if transactions run out of fuel. Thus, it might be simpler to not trouble with continuations, and fairly decide for easy one-way messages; as a result of the language is Turing-complete continuations can all the time be constructed on high.
On account of the inefficiency and instability of cross-chain messages irrespective of how they’re performed, most dapps will wish to dwell totally within a single sub-state, and dapps or contracts that ceaselessly discuss to one another will wish to dwell in the identical sub-state as properly. To stop completely everybody from dwelling on the identical sub-state, we are able to have the fuel limits for every substate “spill over” into one another and attempt to stay related throughout substates; then, market forces will naturally be certain that fashionable substates develop into dearer, encouraging marginally detached customers and dapps to populate contemporary new lands.
Not So Quick
So, what issues stay? First, there may be the info availability drawback: what occurs when all the full nodes on a given sub-state disappear? If such a scenario occurs, the sub-state knowledge disappears without end, and the blockchain will basically must be forked from the final block the place all the sub-state knowledge truly is thought. It will result in double-spends, some damaged dapps from duplicate messages, and so on. Therefore, we have to basically ensure that such a factor won’t ever occur. This can be a 1-of-N belief mannequin; so long as one trustworthy node shops the info we’re wonderful. Single-chain architectures even have this belief mannequin, however the concern will increase when the variety of nodes anticipated to retailer each bit of information decreases – because it does right here by an element of 2048. The priority is mitigated by the existence of altruistic nodes together with blockchain explorers, however even that may develop into a problem if the community scales up a lot that no single knowledge middle will be capable of retailer all the state.
Second, there’s a fragility drawback: if any block wherever within the system is mis-processed, then that might result in ripple results all through all the system. A cross-substate message won’t be despatched, or is likely to be re-sent; cash is likely to be double-spent, and so forth. In fact, as soon as an issue is detected it could inevitably be detected, and it could possibly be solved by reverting the entire chain from that time, however it’s totally unclear how typically such conditions will come up. One fragility answer is to have a separate model of ether in every substate, permitting ethers in numerous substates to drift in opposition to one another, after which add message redundancy options to high-level languages, accepting that messages are going to be probabilistic; this may enable the variety of nodes verifying every header to shrink to one thing like 20, permitting much more scalability, although a lot of that may be absorbed by an elevated variety of cross-substate messages doing error-correction.
A 3rd challenge is that the scalability is restricted; each transaction must be in a substate, and each substate must be in a header that each node retains observe of, so if the utmost processing energy of a node is N transactions, then the community can course of as much as N2 transactions. An method so as to add additional scalability is to make the hypercube construction hierarchical in some vogue – think about the block headers within the header chain as being transactions, and picture the header chain itself being upgraded from a single-chain mannequin to the very same hypercube mannequin as described right here – that may give N3 scalability, and making use of it recursively would give one thing very very like tree chains, with exponential scalability – at the price of elevated complexity, and making transactions that go all the way in which throughout the state house rather more inefficient.
Lastly, fixing the variety of substates at 4096 is suboptimal; ideally, the quantity would develop over time because the state grew. One possibility is to maintain observe of the variety of transactions per substate, and as soon as the variety of transactions per substate exceeds the variety of substates we are able to merely add a dimension to the dice (ie. double the variety of substates). Extra superior approaches contain utilizing minimal minimize algorithms such because the comparatively easy Karger’s algorithm to attempt to break up every substate in half when a dimension is added. Nonetheless, such approaches are problematic, each as a result of they’re advanced and since they contain unexpectedly massively rising the price and latency of dapps that find yourself by accident getting minimize throughout the center.
Different Approaches
In fact, hypercubing the blockchain is just not the one method to creating the blockchain scale. One very promising various is to have an ecosystem of a number of blockchains, some application-specific and a few Ethereum-like generalized scripting environments, and have them “discuss to” one another in some vogue – in apply, this typically means having all (or a minimum of some) of the blockchains preserve “gentle purchasers” of one another within their very own states. The problem there is determining have all of those chains share consensus, significantly in a proof-of-stake context. Ideally, all the chains concerned in such a system would reinforce one another, however how would one try this when one cannot decide how useful every coin is? If an attacker has 5% of all A-coins, 3% of all B-coins and 80% of all C-coins, how does A-coin know whether or not it is B-coin or C-coin that ought to have the higher weight?
One method is to make use of what is actually Ripple consensus between chains – have every chain determine, both initially on launch or over time through stakeholder consensus, how a lot it values the consensus enter of one another chain, after which enable transitivity results to make sure that every chain protects each different chain over time. Such a system works very properly, because it’s open to innovation – anybody can create new chains at any level with arbitrarily guidelines, and all of the chains can nonetheless match collectively to bolster one another; fairly probably, sooner or later we might even see such an inter-chain mechanism current between most chains, and a few giant chains, maybe together with older ones like Bitcoin and architectures like a hypercube-based Ethereum 2.0, resting on their very own merely for historic causes. The thought right here is for a very decentralized design: everybody reinforces one another, fairly than merely hugging the strongest chain and hoping that that doesn’t fall prey to a black swan assault.


